Start where the risk is
The strongest use cases sit close to likely attacker paths, sensitive workflows, or places where visibility currently drops away.
Representative ways teams use FIRCY Sense
Attack paths worth instrumenting earlier
Earlier warning creates the most value where attacker paths, identity misuse, cloud exposure, and internal movement are hardest to see until it is too late.
The strongest use cases sit close to likely attacker paths, sensitive workflows, or places where visibility currently drops away.
A use case is stronger when the signal arrives with enough context to support triage, hunting, escalation, or automation.
Teams can begin with one high-value use case, then expand coverage across cloud, identity, applications, and internal environments.
Three common starting points
Create earlier visibility around exposed services, application paths, edge infrastructure, and reconnaissance activity before real systems are touched more directly.
Add discreet controls around credentials, access paths, approvals, and identity workflows so suspicious use stands out sooner.
Make internal exploration, lateral movement, and access to sensitive workflows more visible once an attacker has entered the environment.
Representative scenarios
Create earlier warning around quiet scanning, low-noise probing, and suspicious interaction with exposed services, pages, APIs, and paths.
Expose suspicious interaction with planted credentials, access paths, or identity lures so teams gain a clearer signal when credentials are being tested, reused, or moved with.
Create controlled interaction points inside the environment so suspicious discovery, service access, and lateral movement attempts are easier to identify and scope.
Introduce early-warning coverage around selected application paths, interfaces, and services so suspicious behaviour is detected sooner and reviewed with stronger context.
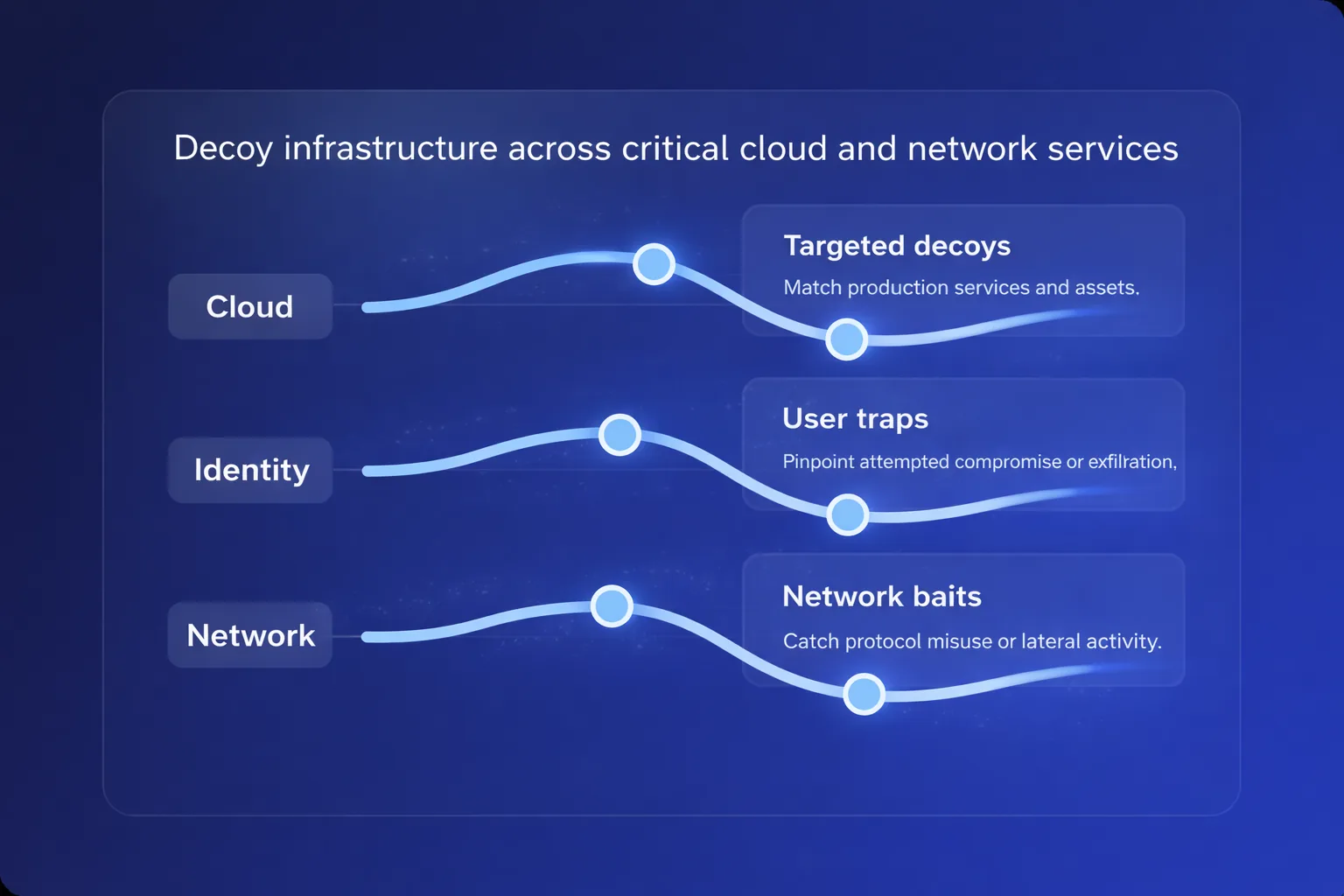
Place realistic early-warning controls where cloud, SaaS, and hybrid attack paths intersect identities, workloads, exposed services, and management planes.
Add discreet visibility around workflows where the cost of late detection is high, including sensitive data paths, privileged operations, or critical internal services.
Common cyber deception use cases
Decoy credentials and identity-related lures can help expose account compromise, credential testing, privilege exploration, or misuse of access paths that should not be touched during normal operations.
Deception signals placed around internal systems, applications, and sensitive paths can reveal reconnaissance, service discovery, attempted movement, or unusual access behaviour before an attacker reaches critical assets.
Synthetic documents, workflows, services, or access paths that appear valuable can help reveal suspicious interaction by staff, contractors, service accounts, or compromised identities.
Canary-style signals are useful when they are tied to a broader detection strategy and include context about what was accessed, where the interaction came from, and how the event should be handled.
Cloud and application deception can be placed around export paths, synthetic customers, reports, admin functions, API references, and other high-value workflows to reveal suspicious access earlier.
What strong use cases deliver
Reveal suspicious activity before attackers reach more valuable systems, data, or workflows.
Give analysts alerts that are worth investigating rather than more background noise.
Generate practical context that supports triage, hunting, escalation, and decision-making.
Connect early warning to the controls and teams responsible for defensive action.
Operating model
Different organisations need different operating models. FIRCY Sense can support a managed service, a co-managed rollout, or a self-managed deployment.
Move quickly when internal bandwidth is limited and you want early warning, intelligence, and guidance delivered with less overhead.
Share ownership while building internal confidence, workflows, and coverage over time.
Operate the platform inside your environment when control, locality, or internal ownership matter most.
Context
Make it specific