Notify the right people
Push meaningful events to the channels and teams that already handle investigation and response.
Operational fit matters
From signal to action
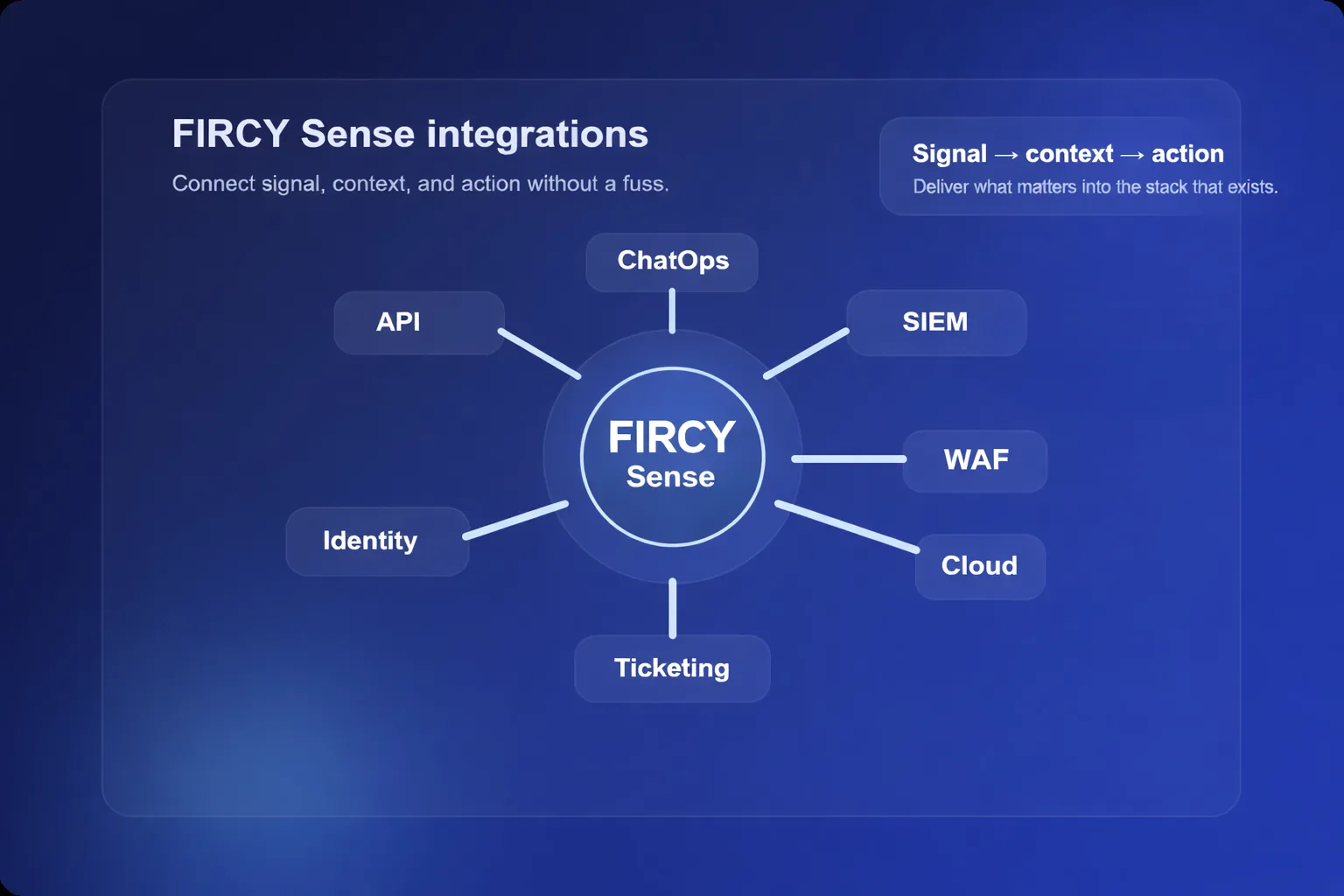
The goal is to move high-confidence signal into the systems your team already trusts, without adding another operational silo.
Push meaningful events to the channels and teams that already handle investigation and response.
Add high-confidence threat intelligence to SIEM, case, and hunting workflows instead of creating another silo.
Use APIs, webhooks, and existing WAF or response controls to move from signal to triage, escalation, or defensive response.
Common integration patterns
Surface meaningful events in Slack, Microsoft Teams, email, or internal workflows so the right people see them quickly.
Send context into SIEM, analytics, case, and hunting workflows so detections arrive with more operational value.
Trigger webhooks, orchestration, or downstream WAF and response actions when suspicious interaction meets the right threshold.
Fit FIRCY Sense into your current operating model rather than reshaping your team around a new console.
From signal to workflow
Send high-confidence deception events into SIEM platforms such as Microsoft Sentinel, Splunk, and similar analytics environments for investigation and correlation.
Open SOAR, case, or ticketing workflows when a signal is triggered so analysts have a clear path from detection to follow-up.
Attach identity, application, cloud, source, and interaction context so responders can understand why the event matters.
Notify analysts through collaboration or incident response channels without losing the context that makes the signal useful.
Trigger defensive actions through WAF, edge, cloud, or custom automation controls where policy and workflow design call for it.
Familiar ecosystems
Representative examples only. The exact delivery pattern depends on your stack, workflow design, and how deeply you want detections, intelligence, and response to connect.
Where integrations usually matter
Send meaningful events into the channels where analysts, responders, or engineers already coordinate.
Feed detections and context into analytics workflows so teams can correlate early warning with broader telemetry.
Create operational follow-through by routing detections into issue tracking and case workflows.
Fit FIRCY Sense into the environments where modern attack paths cross cloud platforms, edge services, and existing WAF controls.
Route identity-relevant signals into the teams and systems responsible for authentication, access, and privileged workflows.
Use APIs and webhooks to trigger enrichment, escalation, or defensive workflows that match your internal operating model.
WAF and edge response
Update approved Cloudflare policy inputs so existing rules can apply the configured response, with supporting telemetry available for review.
Feed detections into approved AWS WAF policy inputs so your existing Web ACL remains the enforcement path and reporting stays within familiar workflows.
Update nominated Azure Front Door WAF policy inputs so response follows the existing edge policy model you already govern.
The aim is to let early warning trigger action through controls you already own and govern.
Example patterns
A meaningful event lands in a collaboration channel with enough context for an analyst to validate, investigate, and escalate quickly.
Earlier warning from exposed paths, workloads, or edge environments is correlated with broader telemetry and can feed existing WAF or edge controls when the configured policy calls for it.
Identity-related interaction becomes a trigger for additional review, escalation, or active defence through existing workflows.
What effective integration looks like
Meet teams where they already work instead of forcing a greenfield operating model.
Make sure signals arrive with the detail needed for action, not just a notification.
Start lightweight if needed, then deepen integration where it creates real operational value.
Build towards useful action rather than stopping at passive alerting.
Make the stack work harder